PHP 5.6 available on our Cloud VPS platform
Over a year after PHP 5.5 was released, the latest and greatest version 5.6 has just arrived and is already supported on our fully managed Cloud VPS hosting platform.
New features in our PHP 5.6 hosting
Here are some of the highlights of this new version of PHP:
-
Constant scalar expressions: you can now provide static scalar expressions, so you can now use static expressions (in the past you could only use static values), e.g. in function arguments, const declarations or property declarations;
-
Memory usage using POST has been reduced;
-
An interactive debugger called phpdbg has been implemented – you can access it from the command line to debug your code step-by-step;
-
Uploads of over 2GB are now accepted (but check you have enough server resources before doing this!);
-
php://input is now reusable;
-
Many SSL/TLS improvements such as protection against attacks, improved peer verification, fingerprinting SSL certificates, and significant enhancements when using encrypted streams;
Transfer the environment not just the project
At Layershift we’re always looking for new ways to help you to be more efficient and productive. After all, Jelastic is the PaaS for people aiming for success; you don’t get to be successful by wasting your time repeating your work or grappling with awkward configurations!
We received lots of great feedback (thanks!) following the recent overhaul of our environment collaboration feature – allowing you to get the whole team working within 1 Jelastic account, and sharing individual environments with appropriate team members.
You told us loud and clear that it’s immensely helpful to have this convenient way to temporarily share an environment with a freelancer or agency. But, you said, what about when the freelancer starts the project off on the Jelastic platform and wants to hand ownership over to his client at the end? There should be a good way to handle that situation…
Well yes, we completely agree. Here it is!
Generating Jelastic SSH keys with PuTTYgen
We’ve just added key-based SSH access to our Jelastic PaaS, and with many of our Windows users using PuTTY as their preferred SSH client it seems a good moment to give a brief PuTTYgen walkthrough. Here’s how to generate SSH keys using PuTTY.
1. Download and open puttygen.exe (included with putty-version-installer.exe, or standalone)
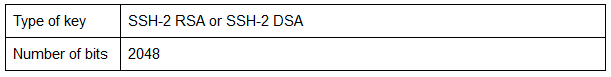
2. Enter the following parameters (the defaults are fine):
How to Tune the Garbage Collector in Tomcat
The guys at PayPal recently switched away from Java, citing (perhaps false/questionable ?) performance gains. One important, but easily overlooked, way to keep your Java app performing at its best is to make sure that the JVM is well tuned to your needs – that includes taming the Garbage Collector.
If Java had true garbage collection, most programs would delete themselves upon execution.
– Robert Sewell
Java’s Garbage Collector does an important job, and if you tune it properly, you can prevent memory intensive programs from freezing your system. It’s easy to assume that if you know how to develop large programs and applications, you probably already know how the Garbage Collection process works. Ergo if you choose the right Garbage Collector algorithm, it means you totally understand the features of the program you have developed.
If you’re not quite sure how the whole process works, we’ll try to summarise the most important aspects for you.
Meet the Garbage Collector, it will save your day!
You’ve just developed a large application, and you couldn’t be more excited! But, as this application runs, it creates objects; as it continues to run, many of these objects are no longer required and they cause your program to run out of memory for no apparent reason.
Secure your mailbox with powerful email antivirus protection!
If you’re one of our Cloud VPS customers and are looking to protect your hosted cloud email from viruses, you’ve probably heard about Parallels Premium Antivirus by Dr. Web already.
Dr. Web is what keeps your mailbox safe from all the naughty viruses out there. With more than two decades experience (Doctor Web started developing the anti-virus software in the early 1990’s) the developers have come up with a very effective heuristic engine, and comprehensive virus definitions database (over 120,000 definitions, and each individual definition can detect up to thousands of viruses!). Their sophisticated heuristic virus analysing engine with fly-code technology, origins tracing and structural entropy analysis can detect zero-day viruses and other malware before they are even added to the virus database.
Why do I need to use email antivirus?
Research from the UK’s Federation of Small Businesses estimates that the cost of cybercrime amongst its members in 2012 was £4,000 per member on average (around $6,500) of which virus infections were responsible for a staggering 20%!
According to a study in The Guardian, more than 9 million adults in Britain were hacked in the past year. Would you take this chance?
Another thing worth mentioning is spam generated from your computer becoming infected by viruses. It’s common for a virus to ‘hijack’ your computer to send outbound spam – and we all know everyone hates receiving spam! GroupIB, specialists in cyber security, made a recent report about the evolution of spam in the last two years and determined that profits gained worldwide from this activity reached $786 million in 2012. The main products targeted by these spamming campaigns were medicines, drugs or software. What would your customers say if they suddenly received slimming advice from your e-mail account? Not very professional, right? The only thing ‘slimmed’ would be your profits!
How it works
With Dr Web, you get a rapid protection time for all new viruses. You can be confident it’s up to date with hourly updates – critical during any outbreak! Dr. Web’s over 150 R&D staff work around the clock to keep a constant eye on new viruses and respond as soon as something looks questionable, keeping your inbox protected.